How Robust Data Destruction Enhances Your Overall Cyber Security Steps
How Robust Data Destruction Enhances Your Overall Cyber Security Steps
Blog Article
Exactly How Proper Information Devastation Adds To Robust Computer Safety And Security Solutions and Mitigates Dangers of Information Violations
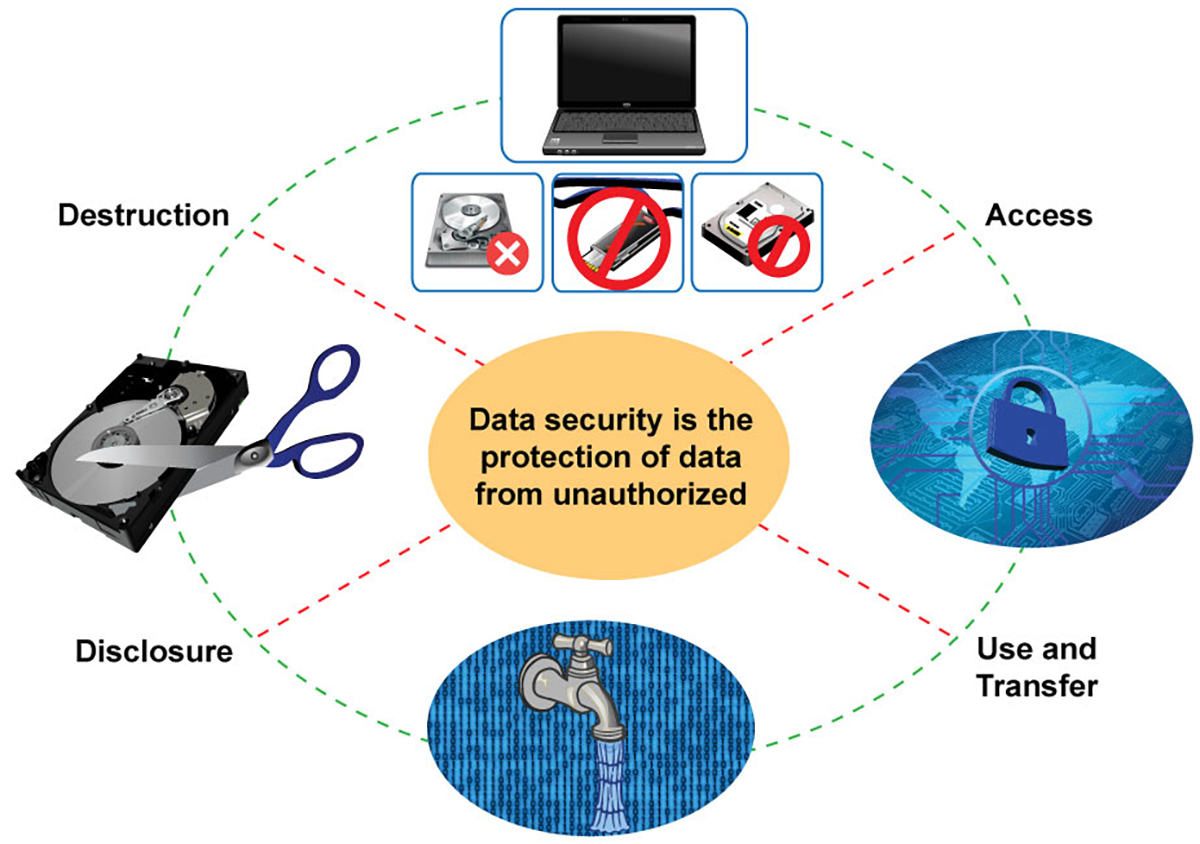
In today's digital landscape, the significance of appropriate information devastation can not be overemphasized, as it serves as a basic part of detailed computer system security solutions. By implementing efficient data erasure methods, companies not only safeguard sensitive info from unauthorized access but additionally bolster their compliance with regulatory structures - data destruction. The implications of insufficient data damage expand beyond simple conformity; they can greatly influence an organization's cybersecurity position and track record. Understanding these dimensions elevates crucial questions concerning the methods in position and their effectiveness in a period of rising cyber hazards.
Importance of Information Damage
In today's electronic landscape, the relevance of information devastation can not be overemphasized. As companies significantly rely upon digital properties, the prospective threats related to information violations and unauthorized accessibility intensify. Effective information devastation is a crucial part of an extensive details safety approach, securing delicate information from coming under the hands of malicious actors.
When information is no more required, simply removing files or formatting disk drives wants. Recurring information can typically be recouped making use of easily offered tools, posturing considerable hazards to both companies and individuals. This emphasizes the requirement for robust information destruction practices that make certain all data is irretrievably erased.
Additionally, regulatory compliance requireds, such as GDPR and HIPAA, highlight the obligation to safeguard sensitive information, including its correct disposal. Non-compliance can lead to serious legal repercussions and punitive damages. data destruction. Thus, integrating efficient data devastation protocols not just enhances safety and security however likewise strengthens a company's track record and reliability

Techniques of Secure Information Erasure
Several efficient techniques of secure information erasure can be employed to make certain that delicate information is completely removed from storage space devices. One commonly identified technique is information overwriting, which involves changing existing data with arbitrary patterns numerous times. This technique considerably minimizes the chances of information recovery, although it might not be reliable against advanced forensic techniques.

Physical destruction is also a reputable strategy, where storage gadgets are provided pointless with shredding, squashing, or incineration. This approach ensures that information can not be recouped whatsoever but calls for cautious handling of harmful materials.
Finally, specialized software application tools created for safe and secure data erasure give capabilities that abide by different erasure criteria. These tools commonly include features like confirmation procedures to validate effective information destruction.
Employing these methods in mix can enhance information protection and alleviate the threats connected with data violations, guaranteeing that delicate details is not unintentionally exposed.
Legal and Conformity Considerations
The techniques utilized for protected information erasure not just serve to protect delicate info yet also must line up with legal and compliance frameworks governing information security. Organizations are required to stick to various regulations, such as the General Information Protection Regulation (GDPR), the Wellness Insurance Coverage Portability and Liability Act (HIPAA), and the Payment Card Sector Data Safety And Security Criterion (PCI DSS) These guidelines mandate certain methods for official source information handling and devastation, guaranteeing that sensitive and individual data is irretrievably eliminated when no more needed.
Failing to follow these legal requirements can result in considerable penalties, consisting of penalties and reputational damage. Furthermore, organizations must preserve documents of data devastation processes, demonstrating compliance throughout audits or investigations. This documents not only protects against lawful repercussions however likewise reinforces depend on with stakeholders and consumers, showcasing a dedication to information security.
Including lawful and compliance factors to consider into information damage practices is essential for any type of organization. It decreases the risk of data violations and highlights a proactive strategy to securing delicate info, inevitably fostering a culture of protection and liability across the company.
Influence On Cybersecurity Position
Effective data damage dramatically enhances a company's cybersecurity pose by decreasing the potential assault surface for cyber risks. When delicate data is not correctly destroyed, it continues to be easily accessible to harmful stars who can manipulate this info for unapproved access, identification theft, or business espionage. By applying durable information damage procedures, organizations can properly minimize the danger of information violations and improve their total safety structure.
In addition, the secure disposal of outdated or unneeded data not just shields delicate details but also assists companies comply with sector laws and criteria. Failure to effectively damage data can bring about severe lawful effects and reputational damages, additional jeopardizing an organization's cybersecurity position.
Ultimately, focusing on reliable data devastation is vital for cultivating a robust cybersecurity pose, making sure that organizations remain attentive versus advancing cyber threats while shielding their essential properties and stakeholders.
Best Practices for Organizations
Carrying out ideal practices useful source for information damage is important for organizations aiming to secure sensitive info and alleviate cybersecurity risks. Companies should develop a detailed information devastation policy that outlines responsibilities and treatments. This plan needs to comply with relevant policies, such as GDPR or HIPAA, making sure legal consistency.
Second of all, it is important to make use of accepted data sanitization techniques, consisting of data cleaning, degaussing, and physical damage, tailored to the type of data and storage space medium. Employing certified experts for information devastation services improves the dependability of these techniques.
Additionally, organizations should maintain a comprehensive inventory of all information storage space gadgets, ensuring that all out-of-date or changed devices undertakes devastation. Normal audits of data devastation practices can assist determine weak points and boost conformity.
Staff member training is an additional essential aspect, as staff needs to understand the significance of information damage and abide by established protocols. Finally, companies need to record all data devastation activities to give accountability and traceability, which can be invaluable throughout audits or in case of a violation.
Conclusion

One commonly identified technique is data overwriting, which entails replacing existing information with arbitrary patterns several times.The techniques utilized for protected data erasure not only offer to protect delicate details but also must align with lawful you could try this out and conformity frameworks controling information protection. These regulations mandate specific methods for data managing and damage, guaranteeing that sensitive and personal information is irretrievably removed when no longer needed.
By executing durable information damage protocols, organizations can effectively reduce the danger of data breaches and boost their general safety and security framework.
In final thought, proper information damage is crucial for improving computer safety and security services and reducing the dangers associated with data breaches. - data destruction
Report this page